Pen Test vs. Vulnerability Scan: What’s the Difference and Why You Need Both
When it comes to protecting your business from cyber threats, you might have heard terms like “pen test” and “vulnerability scan” thrown around. But what do they mean? And more importantly, what’s the difference between the two?
Public vs. Private IP Addresses: What’s the Difference?
Most people have heard of an IP address, but do you know what it really is? Or that there are two different kinds? There's a public IP address and a private IP address. Here's the difference between them.
How the Industrial Internet of Things (IIoT) is Transforming Industry Operations
The Industrial Internet of Things (IIoT) is transforming the way industries operate, bringing the power of connectivity and data analysis to manufacturing, energy, transportation, and other industrial sectors. But what exactly is IIoT, and why is it such a game-changer?
How to Leverage Microsoft 365 Copilot for Your Small Business
Microsoft has expanded the availability of one of its most dynamic tools to SMBs. A tool that can be a real game-changer for growth. Copilot for Microsoft 365 is a powerful new addition to the M365 suite. It was first offered to enterprise customers only. But Copilot is now open to businesses of all sizes as long as they have Microsoft 365 Business Standard or Business Premium.
How Does The Internet Of Things (IoT) Work?
Your business is a complex ecosystem where different devices, machines, and systems interact to perform various tasks. Now, think about connecting all these devices to the internet, allowing them to communicate, collect data, and make decisions autonomously. That's essentially what the Internet of Things (IoT) is all about.
What Makes a Smart City Smart?
A smart city is a city that uses technology and data to improve the lives of its residents and make urban living more efficient, sustainable, and enjoyable. But what makes the city "smart?" and while technology improvements offer many benefits, what are the potential issues if safety measures aren't in place?
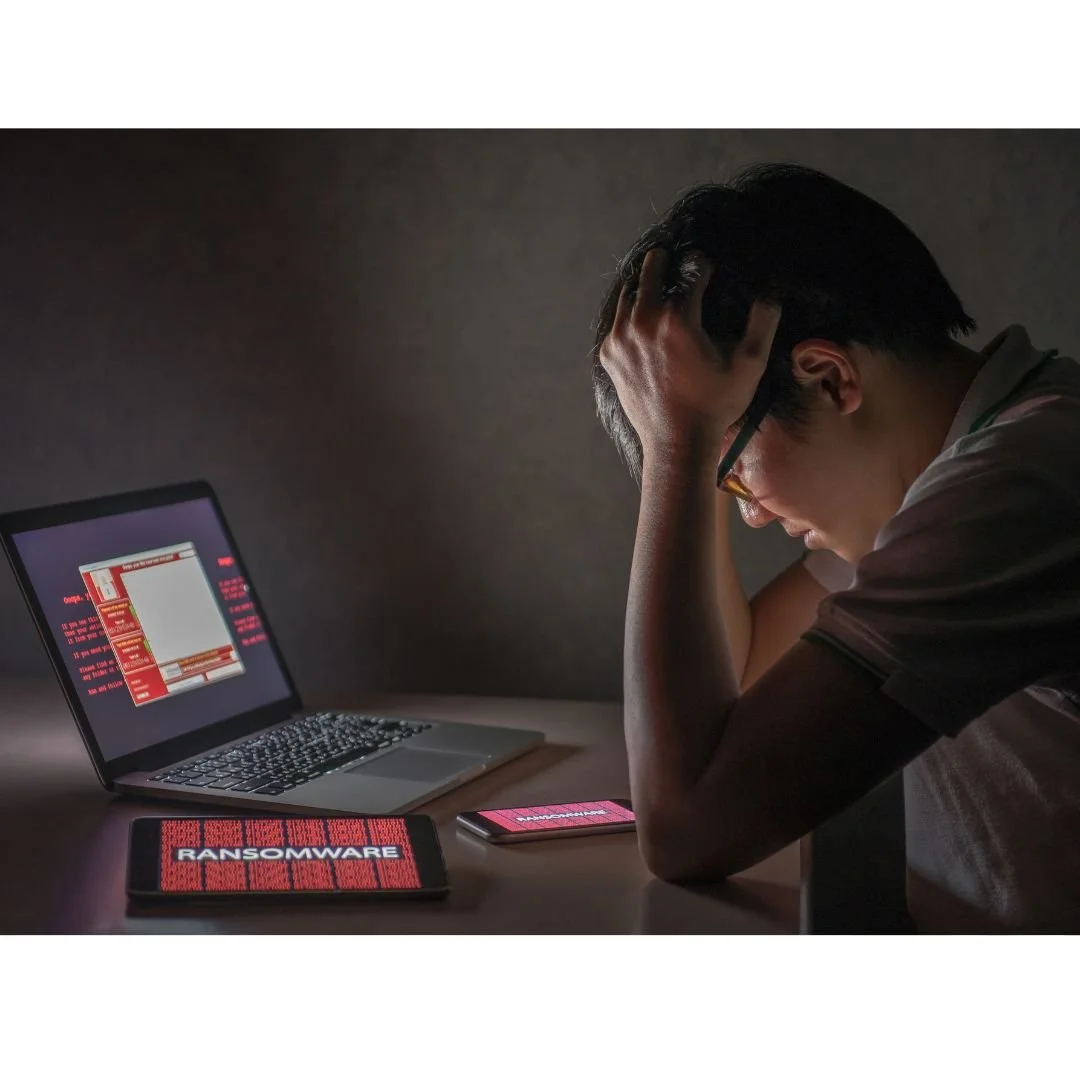
What Should You Do About Ransomware?
Ransomware is a type of malware that hackers use to encrypt your files or lock you out of your own computer or device. Once your files are encrypted or your device is locked, the cybercriminals demand a ransom payment from you, usually in cryptocurrency like Bitcoin, in exchange for the key or code to unlock your files or device.
What is Network Monitoring and How Does It Work?
Network monitoring is the process of observing and analyzing the traffic and behavior of computer networks to ensure they are performing optimally and securely. They make sure everything is in order and there are no suspicious activities or potential threats.
VR, AR, and MR…What Are They?
In recent years, technology has rapidly changed the way we interact with the digital world. There are two terms that have been used over the past few years that may sound familiar. VR, Virtual Reality, and AR, or Augmented Reality. One you probably haven’t heard of as much is MR, or Mixed Reality.